TLP:WHITE — Unrestricted Distribution within the Security Community

Independent Validation, Certificate History & Expanded Driver Arsenal
dragoncore_k.sys | Zhengzhou 403 Network Technology | Cert Graveyard Collaboration
| Field | Value |
|---|---|
| Report Date | April 29, 2026 |
| Authors | Alex Necula (Ransom-ISAC) |
| Independent Researcher Credit | Michael Haag — Principal Threat Research Engineer, Splunk / @M_haggis |
| Certificate Reporting Platform | Cert Graveyard — Community certificate abuse reporting project by Squiblydoo |
| Part I | DragonBreath: Dragon in the Kernel — Ransom-ISAC, April 22, 2026 |
| TLP Classification | TLP:WHITE — Unrestricted Distribution |
Overview
Following the publication of Part I, Michael Haag (Principal Threat Research Engineer, Splunk) contacted the authors to share that he had independently reported the same Zhengzhou 403 certificate to GlobalSign on May 1, 2025 — nearly a year before Part I was published, and through an entirely separate investigation path.
His report, submitted via the Cert Graveyard community reporting platform, directly triggered the explicit revocation by GlobalSign documented in Part I. Three independent investigators — the Part I authors, Michael Haag, and the MalwareBazaar community tagging — all converged on the same certificate, the same C2 infrastructure, and the same abuse pattern without coordination. This constitutes robust multi-source confirmation.
Beyond validating the Part I findings, Michael's report introduced evidence that had not yet been documented: a prior Zhengzhou 403 EV certificate active from January 2024, and two additional malicious drivers signed under it — including a process-hiding driver compiled directly from a public GitHub rootkit repository, and YDArkDrv.sys, a well-known Chinese offensive kernel toolkit. Together, these findings expand the Zhengzhou 403 operational picture from a single driver to a complete layered kernel-level offensive stack active for over 15 months.
1. Michael Haag's Independent Report to GlobalSign (May 1, 2025)
Michael Haag submitted the following abuse report to GlobalSign on May 1, 2025, using the Cert Graveyard reporting toolchain (certReport):
Greetings,
We identified a malware signed with a GlobalSign GCC R45 EV CodeSigning CA 2020 certificate.
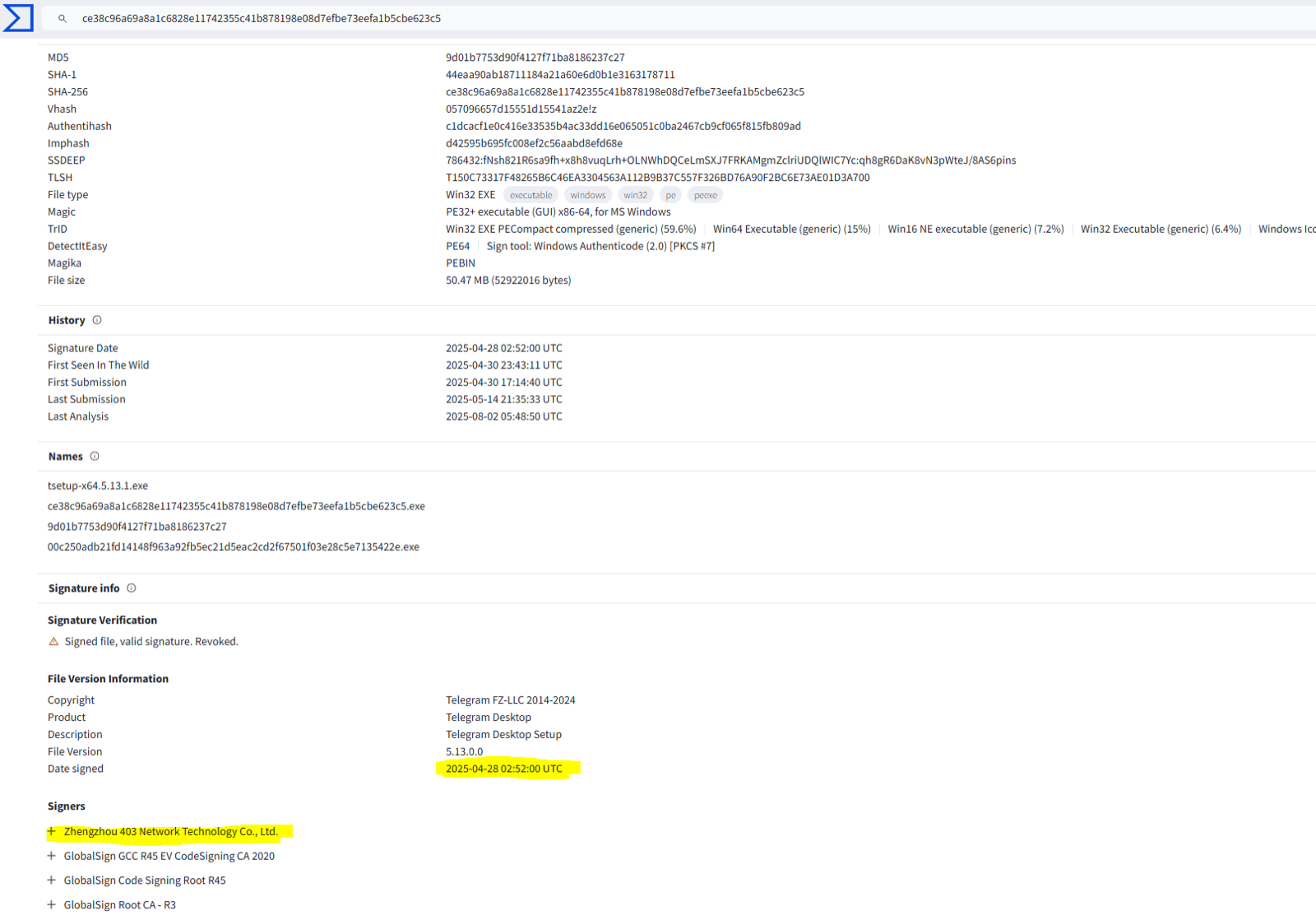
The malware sample is available on VirusTotal: https://www.virustotal.com/gui/file/ce38c96a69a8a1c6828e11742355c41b878198e08d7efbe73eefa1b5cbe623c5/detection
Certificate details:
- Name: Zhengzhou 403 Network Technology Co., Ltd.
- Issuer: GlobalSign GCC R45 EV CodeSigning CA 2020
- Serial Number:
46 68 ED FA 62 35 54 CF 0B 48 F4 01 - Thumbprint:
B3BD6E706137ED999BFD6E51FE05FCA30C553C30 - Status: Valid (at time of report)
- Valid From: 08:44 AM 03/28/2025
- Valid Until: 08:44 AM 03/29/2026
VirusTotal extracted a malware config for CobaltStrike. It was configured to communicate with the C2 domain oss-aws[.]1nb[.]xyz. This is a trojanized Telegram installer. In sandbox analysis, it uses PowerShell to exclude directories from Windows Defender analysis: powershell -Command "Add-MpPreference -ExclusionPath 'C:\Program Files (x86)\Common Files\System\*'"
Sandbox: https://app.any.run/tasks/d59af4e9-9591-4eaa-9f79-404b411041f3
In reviewing the subscriber, I also observed they had a previous GlobalSign certificate:
- Name: Zhengzhou 403 Network Technology Co., Ltd.
- Issuer: GlobalSign GCC R45 EV CodeSigning CA 2020
- Serial Number:
7A 06 2E 41 04 BF 96 33 E5 CD AC 31 - Thumbprint:
D2BA5AE97458151B42E0C08B248F28EB918A93CF - Status: Valid (at time of report)
- Valid From: 02:24 AM 01/29/2024
- Valid Until: 02:24 AM 01/29/2025
That certificate was used to sign files that are also malicious.
1.1 Analytical Significance
| Finding | Implication |
|---|---|
Same certificate (4668EDFA...) as dragoncore_k.sys | Multi-source confirmation — identical abuse pattern found independently |
Same C2 (oss-aws.1nb.xyz) | C2 infrastructure cross-validated by independent researcher |
| Trojanized Telegram installer as the reported sample | Confirms certificate was used across multiple simultaneous campaigns (LetsVPN + Telegram) — consistent with certificate-as-a-service model |
PowerShell Defender exclusion (Add-MpPreference) | Standard Chinese APT pre-EDR-kill evasion — complements the kernel-level kill capability of dragoncore_k.sys |
| Prior 2024 certificate identified | Extends the Zhengzhou 403 operational timeline back to January 2024 — 15+ months of active malicious signing |
| Report triggered GlobalSign revocation | Michael's May 1, 2025 report is the direct cause of the explicit revocation documented in Part I |
About Cert Graveyard:
Cert Graveyard is a community-driven platform created by Squiblydoo for documenting and reporting code-signing certificate abuse. The platform has processed over 2,000 certificate revocations across major malware families. Michael used the certReport tool to generate and submit this report — the same toolchain that has driven revocations across hundreds of campaigns including SolarMarker, DarkGate, Qakbot, and now Zhengzhou 403. If you encounter a signed malicious file, Cert Graveyard is where to report it: certgraveyard.org.
2. Prior Certificate — January 2024 to January 2025
Michael's report revealed that Zhengzhou 403 held a prior GlobalSign EV certificate active more than a year before the one analyzed in Part I:
| Field | Value |
|---|---|
| Serial Number | 7A062E4104BF9633E5CDAC31 |
| Thumbprint | D2BA5AE97458151B42E0C08B248F28EB918A93CF |
| Valid From | January 29, 2024 |
| Valid To | January 29, 2025 |
| Status | Expired (not explicitly revoked — predates the Cert Graveyard report) |
Critical implication:
Zhengzhou 403 obtained its first EV code-signing certificate from GlobalSign in January 2024 — the operation did not begin in early 2025. Malicious signing activity under this entity spans at least 15 months across two consecutive certificates. The 2024 certificate expired naturally, and a new one was obtained in March 2025 within weeks, demonstrating deliberate operational continuity planning: allow the first certificate to expire without triggering a revocation investigation, then immediately acquire a replacement.
3. Drivers Signed Under the 2024 Certificate
3.1 hide_process Driver — GitHub Rootkit with PDB Path Evidence
| Field | Value |
|---|---|
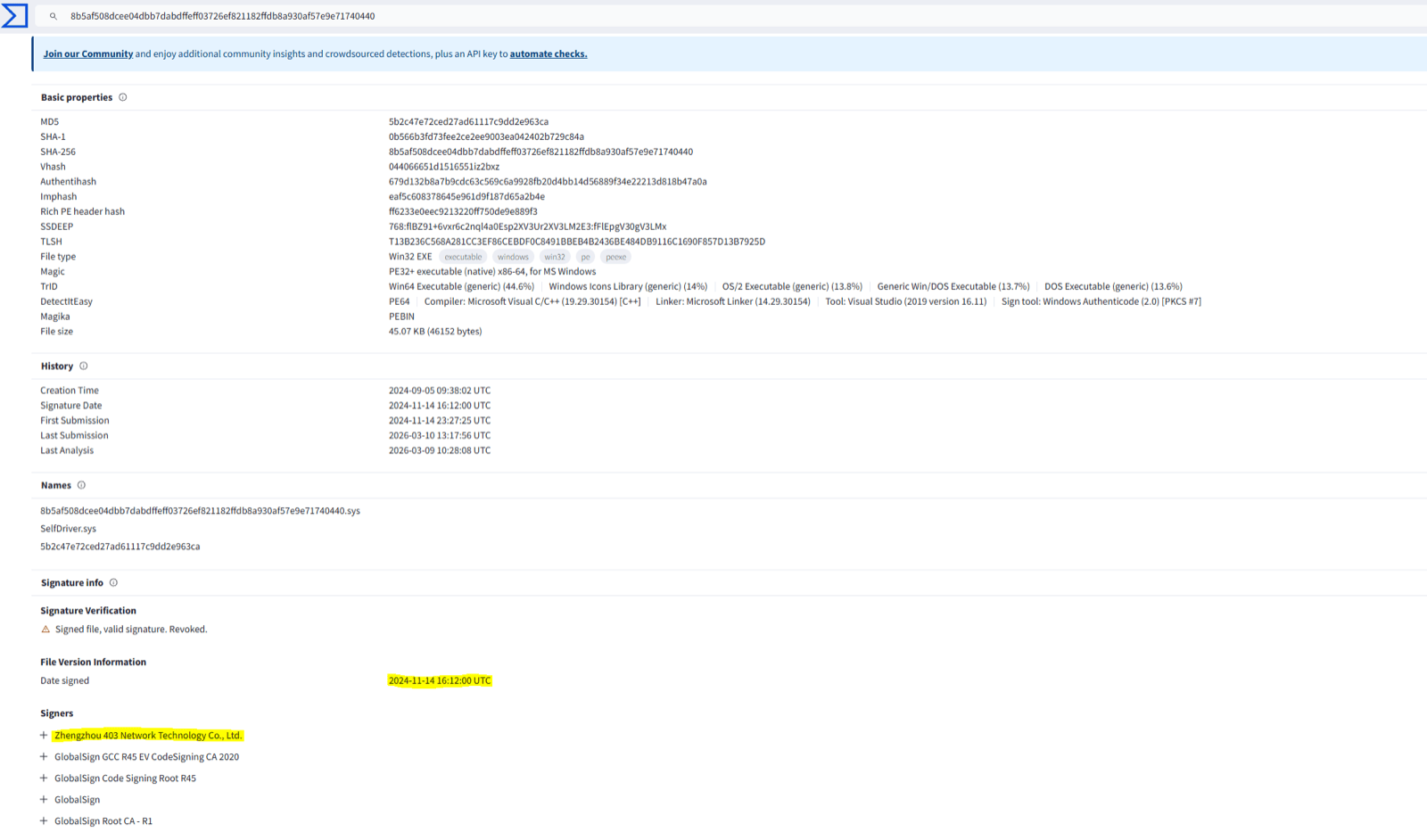
| SHA-256 | 8b5af508dcee04dbb7dabdffeff03726ef821182ffdb8a930af57e9e71740440 |
| Certificate | 7A062E4104BF9633E5CDAC31 (2024 cert) |
| VirusTotal | https://www.virustotal.com/gui/file/8b5af508dcee04dbb7dabdffeff03726ef821182ffdb8a930af57e9e71740440/details |
| PDB Path | C:\Users\Administrator\Desktop\hide_process-master\x64\Release\hide_process.pdb |
What the PDB path reveals:
hide_process-master is a publicly available GitHub repository implementing process hiding via EPROCESS doubly-linked list unlinking — a well-documented kernel rootkit technique. The driver modifies ActiveProcessLinks.Flink and ActiveProcessLinks.Blink in the kernel EPROCESS structure, removing the target process from the list iterated by PsGetNextProcess, ZwQuerySystemInformation, and CreateToolhelp32Snapshot.
A process hidden this way:
- Does not appear in Task Manager, Process Explorer, or any user-mode process enumeration tool
- Does not appear in
tasklist,Get-Process, or WMI queries - Remains detectable only via kernel-level cross-view analysis (EPROCESS vs. handle table comparison)
- Is invisible to
PsSetCreateProcessNotifyRoutineExcallbacks after the unlinking occurs
Operational security observation: The PDB path shows the operator compiled this directly from a cloned GitHub repository on an Administrator desktop (C:\Users\Administrator\Desktop\). This is minimal OpSec on the development machine — consistent with the i-SOON leaked tooling methodology where operators adapt publicly available offensive security research rather than writing tooling from scratch.
Combined capability with dragoncore_k.sys:
When deployed alongside dragoncore_k.sys, these two drivers form a complementary offensive stack:
| Driver | Primary Capability |
|---|---|
dragoncore_k.sys | Kills EDR processes via IOCTL 0x22201C + Spoofs command-line telemetry via PEB write-back |
hide_process driver | Hides the attacker's process entirely from kernel enumeration via EPROCESS unlinking |
Together: blind the security tool, spoof its telemetry, then make the attacker's process disappear from any remaining visibility.
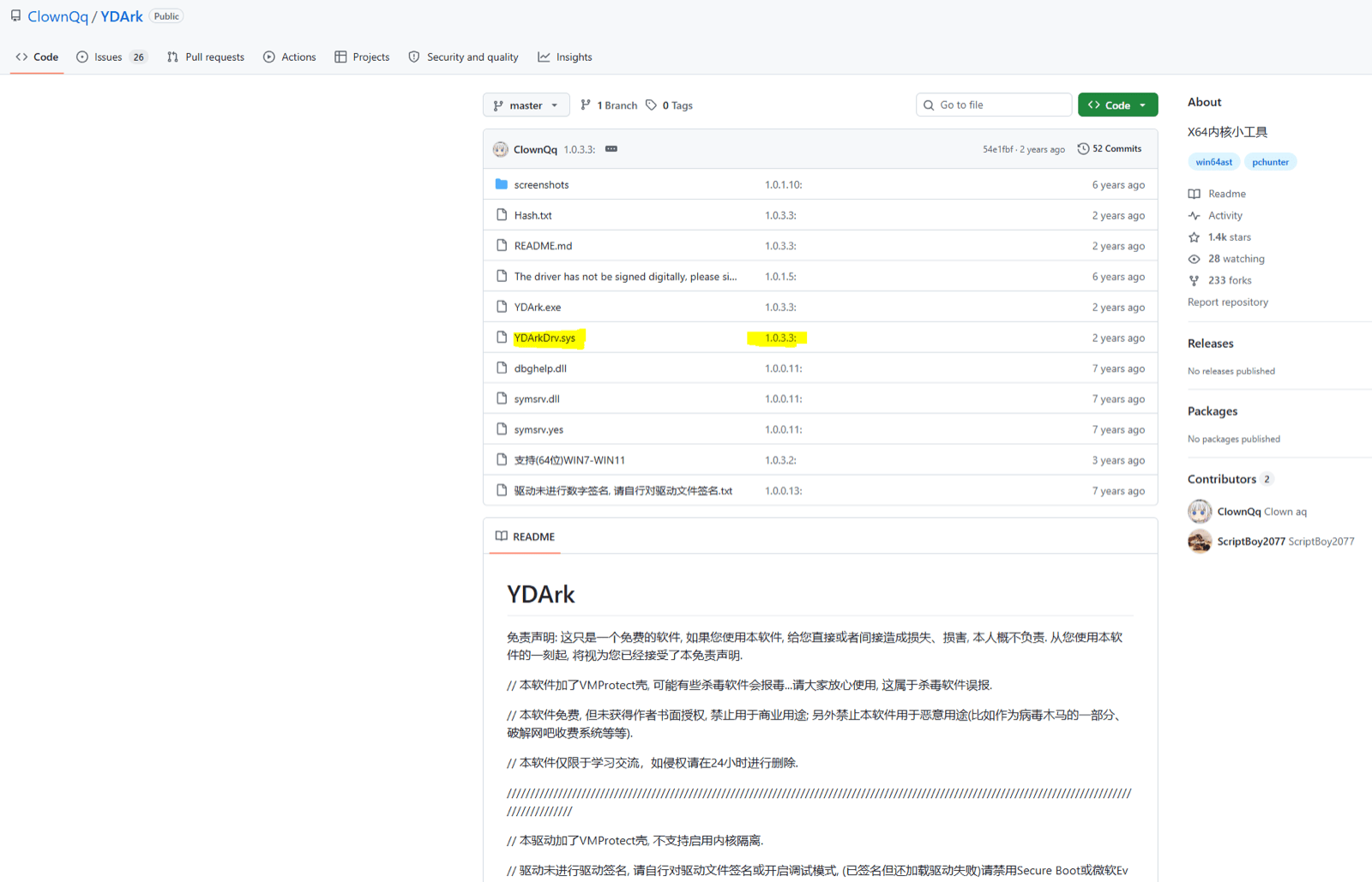
3.2 YDArkDrv.sys — Professional Chinese Rootkit Toolkit
| Field | Value |
|---|---|
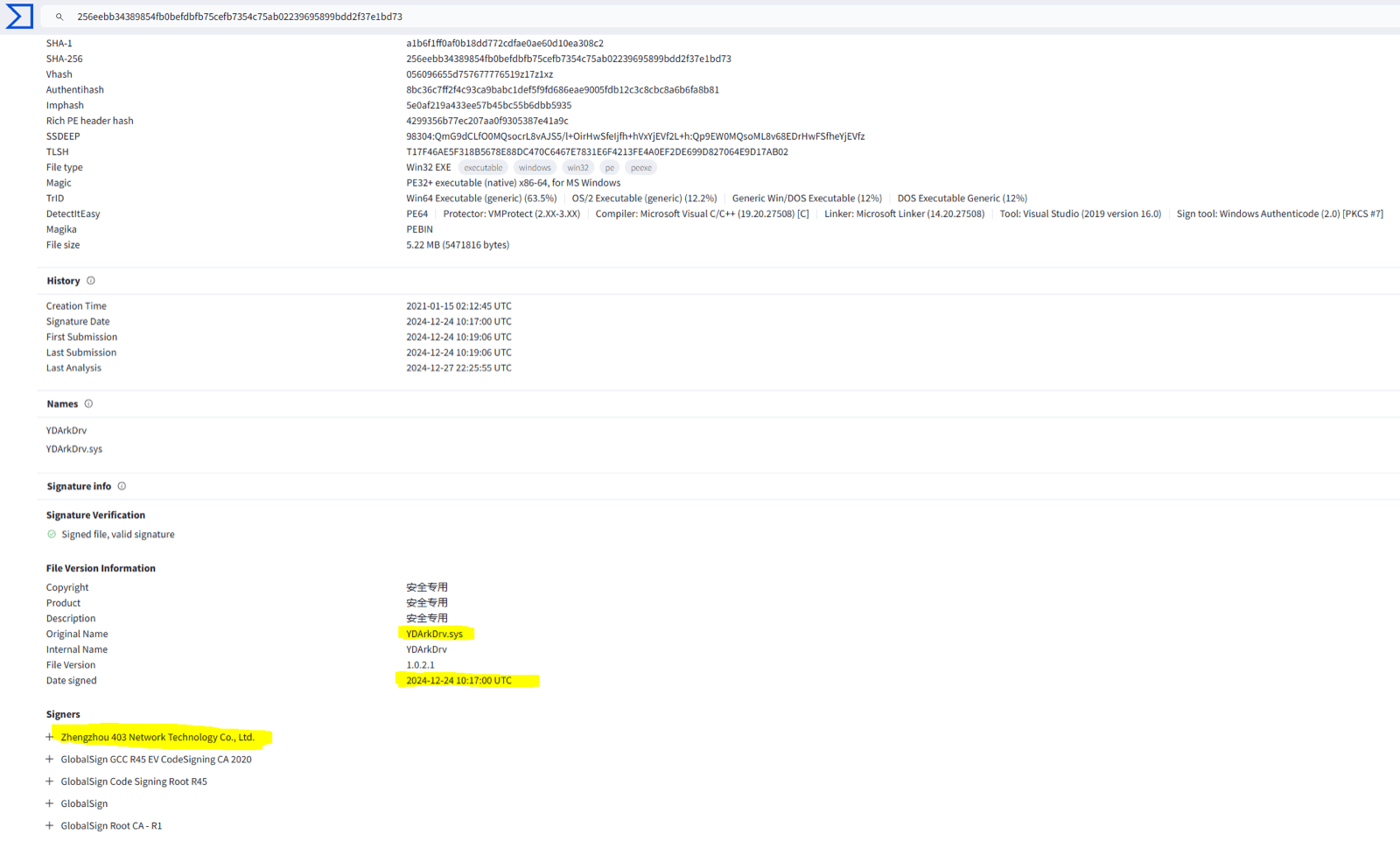
| SHA-256 | 256eebb34389854fb0befdbfb75cefb7354c75ab02239695899bdd2f37e1bd73 |
| Certificate | 7A062E4104BF9633E5CDAC31 (2024 cert) |
| VirusTotal | https://www.virustotal.com/gui/file/256eebb34389854fb0befdbfb75cefb7354c75ab02239695899bdd2f37e1bd73/details |
| Classification | YDArkDrv.sys — kernel driver component of YDArk rootkit toolkit |
YDArk background:
YDArk is a well-documented Chinese offensive security / rootkit toolkit, widely known in Chinese security research communities since 2019. Its kernel driver component YDArkDrv.sys provides a comprehensive suite of system manipulation capabilities:
| Capability | Mechanism |
|---|---|
| Process hiding | EPROCESS.ActiveProcessLinks doubly-linked list unlinking; UniqueProcessId zeroing |
| Process protection | EPROCESS token and protection flags modification |
| Module hiding | PEB InLoadOrderLinks / InMemoryOrderLinks list unlinking |
| File hiding | IRP filter hook on NTFS filesystem |
| Registry hiding | Registry hive direct manipulation |
| SSDT hooking | System Service Descriptor Table function pointer replacement |
| Driver hiding | Driver object list manipulation |
| Arbitrary memory R/W | Direct kernel memory read/write primitives |
| Privilege escalation | Token stealing from System process (SYSTEM token copy) |
Significance:
YDArkDrv.sys is not a proof-of-concept or a simple utility — it is a comprehensive, production-grade offensive kernel toolkit with a high degree of completion. Its presence in the Zhengzhou 403 signing portfolio, alongside a hide_process driver and dragoncore_k.sys, confirms that this certificate was used to build and deploy a deliberate, layered kernel-level offensive capability stack, not isolated accidental samples.
4. The Complete Kernel Offensive Stack
Across both certificates, Zhengzhou 403 signed the following coherent offensive toolkit:
| Layer | Driver | Capability | Certificate |
|---|---|---|---|
| Layer 1 — Kill | dragoncore_k.sys | Terminate EDR/AV via IOCTL 0x22201C (ZwTerminateProcess from Ring 0) | 2025 cert |
| Layer 2 — Blind | dragoncore_k.sys | In-memory PEB CommandLine modification — spoof command-line telemetry across all EDRs | 2025 cert |
| Layer 3 — Hide | hide_process driver | EPROCESS unlinking — remove attacker process from all kernel enumeration | 2024 cert |
| Layer 4 — Full Stealth | YDArkDrv.sys | Files, registry, modules, SSDT, drivers — complete system-wide concealment | 2024 cert |
| Layer 5 — Persist | CobaltStrike Beacon | C2 via oss-aws.1nb.xyz, PowerShell Defender exclusion | 2025 cert (Telegram dropper) |
No legitimate driver development company produces all five layers of this stack under the same EV certificate across 15 months. This is a coordinated offensive toolkit. Zhengzhou 403 Network Technology Co., Ltd. was its signing vehicle.
5. Revised Operational Timeline
| Date | Certificate | Event |
|---|---|---|
| Jan 29, 2024 | 7A062E41... issued | First GlobalSign EV cert obtained by Zhengzhou 403 |
| Jan–Dec 2024 | 7A062E41... active | hide_process driver signed; YDArkDrv.sys signed; additional malicious samples |
| Nov 2024 | 7A062E41... (still active) | dragoncore_k.sys compiled |
| Jan 29, 2025 | 7A062E41... expires | Certificate allowed to expire naturally — no revocation triggered |
| Mar 28, 2025 | 4668EDFA... issued | New EV cert immediately obtained from GlobalSign — seamless operational continuity |
| Mar–Apr 2025 | 4668EDFA... active | dragoncore_k.sys signed; letsvpn-3.12.3.exe signed; trojanized Telegram installer signed |
| May 1, 2025 | — | Michael Haag reports certificate abuse to GlobalSign via Cert Graveyard |
| ~May 2025 | — | GlobalSign explicitly revokes 4668EDFA... — operational window cut to ~5 weeks |
| Apr 22, 2026 | — | Part I published on Ransom-ISAC |
| Apr 29, 2026 | — | Part II published — expanded timeline and driver arsenal documented |
Key pattern:
The natural expiry of the 2024 certificate (rather than revocation) indicates the operator was aware of revocation risk and managed it deliberately. The rapid re-acquisition of a new certificate within 58 days of expiry confirms this was a planned rotation, not a reactive response. Michael Haag's report disrupted the second certificate's operational life — reducing it from a planned 12-month window to approximately 5 operational weeks.
6. Updated Indicators of Compromise
Additional File Hashes
| Filename / Type | SHA-256 | Certificate | Notes |
|---|---|---|---|
| Trojanized Telegram installer | ce38c96a69a8a1c6828e11742355c41b878198e08d7efbe73eefa1b5cbe623c5 | 4668EDFA... (2025) | CobaltStrike C2: oss-aws.1nb.xyz; PowerShell Defender exclusion |
hide_process driver | 8b5af508dcee04dbb7dabdffeff03726ef821182ffdb8a930af57e9e71740440 | 7A062E41... (2024) | PDB: hide_process-master; EPROCESS unlinking |
YDArkDrv.sys | 256eebb34389854fb0befdbfb75cefb7354c75ab02239695899bdd2f37e1bd73 | 7A062E41... (2024) | Full rootkit toolkit |
Additional Certificate (2024)
| Field | Value | Action |
|---|---|---|
| Serial | 7A062E4104BF9633E5CDAC31 | Retroactive hunt across endpoint telemetry — active Jan 2024–Jan 2025 |
| Thumbprint | D2BA5AE97458151B42E0C08B248F28EB918A93CF | Block by thumbprint; files signed remain malicious post-expiry |
| Status | Expired Jan 2025 | Expired ≠ safe — signed files carry the signature permanently |
Additional Behavioral Indicators
- PowerShell
Add-MpPreference -ExclusionPathcommands targetingCommon Files\System\*prior to driver load CreateServiceevents for unsigned or novel kernel drivers immediately following PowerShell Defender exclusion commands- Any process-enumeration anomalies where EPROCESS walking returns different results from
ZwQuerySystemInformation(indicator of EPROCESS unlinking byhide_processorYDArkDrv.sys) - SSDT hook detection via integrity verification of
KeServiceDescriptorTableentries (YDArkDrv.sys indicator)
7. Conclusions
Michael Haag's independent disclosure transforms the Zhengzhou 403 investigation from a single-discovery finding into a multi-investigator, multi-campaign, multi-certificate confirmed operation spanning at least 15 months of active malicious signing activity (January 2024 – May 2025).
The expanded driver arsenal reveals the full picture of what Zhengzhou 403 was actually signing:
dragoncore_k.sys— Kill the EDR, spoof command-line telemetry (Part I)hide_processdriver — Hide the attacker's process from kernel enumerationYDArkDrv.sys— Full system-wide stealth across files, registry, drivers, SSDT- CobaltStrike Beacon — Persistent C2 with Defender exclusion pre-staging
This is not a collection of opportunistic malware samples. It is a coherent, purpose-built offensive toolkit systematically signed under two consecutive EV certificates by a shell company with no legitimate products, registered address confirmed as an uninhabited hotel-floor address, and a founder whose name possibly matches one in APT31 payroll records..
The natural certificate rotation from the 2024 to the 2025 certificate — timed to avoid revocation scrutiny — demonstrates deliberate operational security planning at the certificate infrastructure level. The Cert Graveyard report by Michael Haag disrupted this rotation by triggering an explicit revocation, cutting the second certificate's operational life from a planned 12 months to approximately 5 weeks.
This case demonstrates a model that the community should track systematically:
Chinese APT shell companies acquiring consecutive EV code-signing certificates, rotating on natural expiry to avoid scrutiny, and maintaining continuous malicious signing capability across certificate boundaries. The Cert Graveyard platform exists precisely to close this gap — if you find signed malware, report it at certgraveyard.org.
8. Acknowledgements
Special thanks to Michael Haag (@M_haggis, Principal Threat Research Engineer at Splunk) for independently identifying the Zhengzhou 403 certificate abuse in May 2025, submitting the GlobalSign revocation report that directly triggered the certificate revocation documented in Part I, and sharing his findings with the authors to enable this Part II publication.
Thanks also to Squiblydoo for creating and maintaining Cert Graveyard — the community infrastructure that made it possible to report, track, and revoke this certificate. Without platforms like Cert Graveyard, certificate abuse of this kind would continue undetected for far longer.
9. References
- Part I — Alex Necula, Ellis Stannard — DragonBreath: Dragon in the Kernel — Ransom-ISAC, April 22, 2026 — https://ransom-isac.org/blog/dragonbreath-dragon-in-the-kernel/
- Michael Haag — Independent GlobalSign abuse report, May 1, 2025 — via Cert Graveyard / certReport
- Cert Graveyard — Squiblydoo — Community code-signing certificate abuse reporting platform — https://certgraveyard.org
- Squiblydoo Blog — The CertGraveyard — https://squiblydoo.blog/2026/04/01/the-certgraveyard/
- Michael Haag / Splunk — Threat Research — https://www.splunk.com/en_us/blog/author/mhaag.html
- VirusTotal — Trojanized Telegram sample —
ce38c96a...— https://www.virustotal.com/gui/file/ce38c96a69a8a1c6828e11742355c41b878198e08d7efbe73eefa1b5cbe623c5/detection - VirusTotal —
hide_processdriver —8b5af508...— https://www.virustotal.com/gui/file/8b5af508dcee04dbb7dabdffeff03726ef821182ffdb8a930af57e9e71740440/details - VirusTotal —
YDArkDrv.sys—256eebb3...— https://www.virustotal.com/gui/file/256eebb34389854fb0befdbfb75cefb7354c75ab02239695899bdd2f37e1bd73/details - any.run sandbox — Trojanized Telegram installer analysis — https://app.any.run/tasks/d59af4e9-9591-4eaa-9f79-404b411041f3
- MalwareBazaar — Zhengzhou 403 certificate tag — https://bazaar.abuse.ch/browse/tag/Zhengzhou-403-Network-Technology-Co-Ltd/
- SangYun Shin / Medium — How to Find Processes Hidden by YDArk.exe — https://medium.com/@iamshinsangyun/how-to-find-processes-hidden-by-ydark-exe-18525318164a
- Elastic Security Labs — RONINGLOADER: DragonBreath's New Path to PPL Abuse — November 15, 2025 — https://www.elastic.co/security-labs/roningloader
— END OF PART II —
TLP:WHITE — Approved for unrestricted distribution within the security community.
Disclaimer: For educational and defensive research purposes only. Unauthorized exploitation of described techniques is illegal and unethical.